PRODUCT NEWS
Check out why NG Firewall was recognized as a leader in network security by our customers.
Learn More
NEW PRODUCT RELEASE
The latest release of Micro Edge improves network efficiency with Application Control and Event Reporting.
Learn More
NEW PRODUCT RELEASE
The latest release of NG Firewall improvements include new MFA login option and DHCP Relay.
Learn More

Edge Threat
Management
We take the complexity out of network security—saving you time, money and frustration. Get everything you need in a single, modular platform that fits the evolving needs of your organization without the headaches of multiple vendor solutions.
Simply Powerful Network Security
Edge Threat Management provides IT teams with the ability to ensure protection, monitoring and control for all devices, applications, and events, enforcing a consistent security posture across the entire digital attack surface—putting IT back in control of dispersed networks, hybrid cloud environments, and IoT and mobile devices.
-
NG FIREWALL
Comprehensive Commercial-grade
Network Security Platform -
ETM Dashboard
Cloud-based Centralized
Management Platform -
MICRO EDGE
Lightweight Network-edge Device
for Branch Office Connectivity
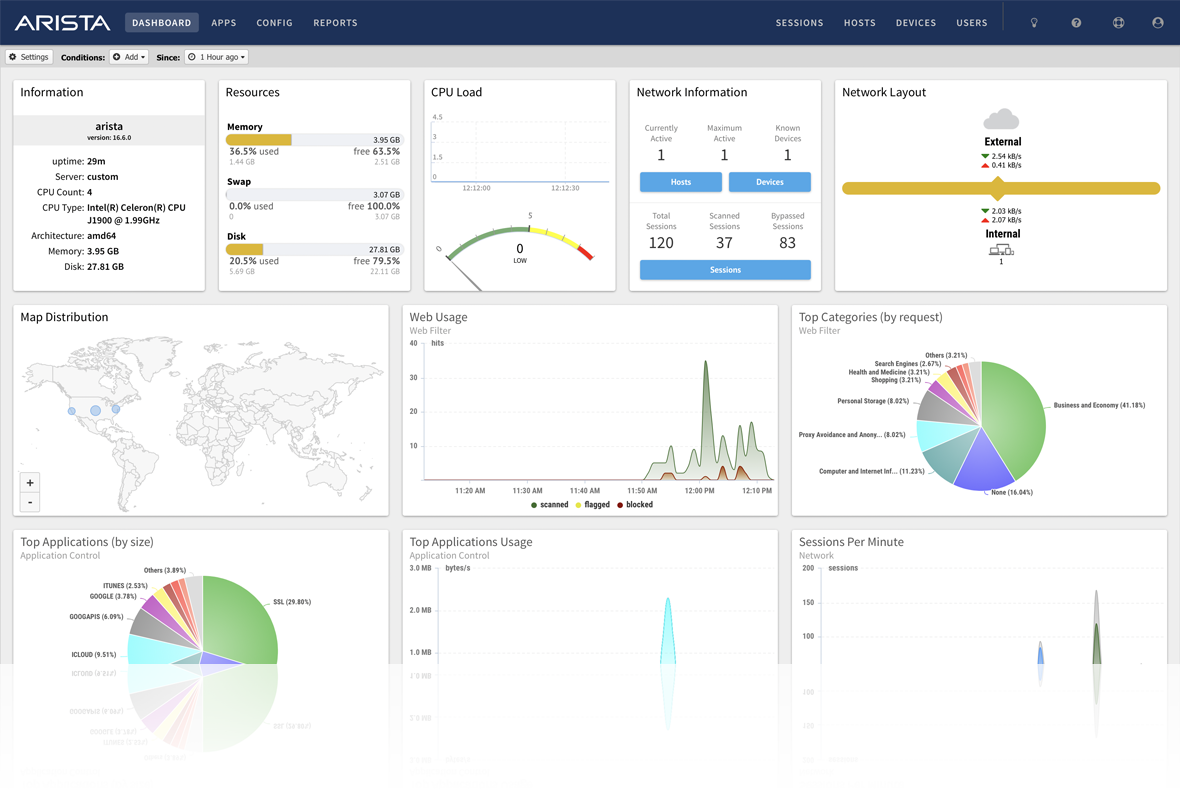
NG FIREWALL
Comprehensive Commercial-grade
Network Security Platform
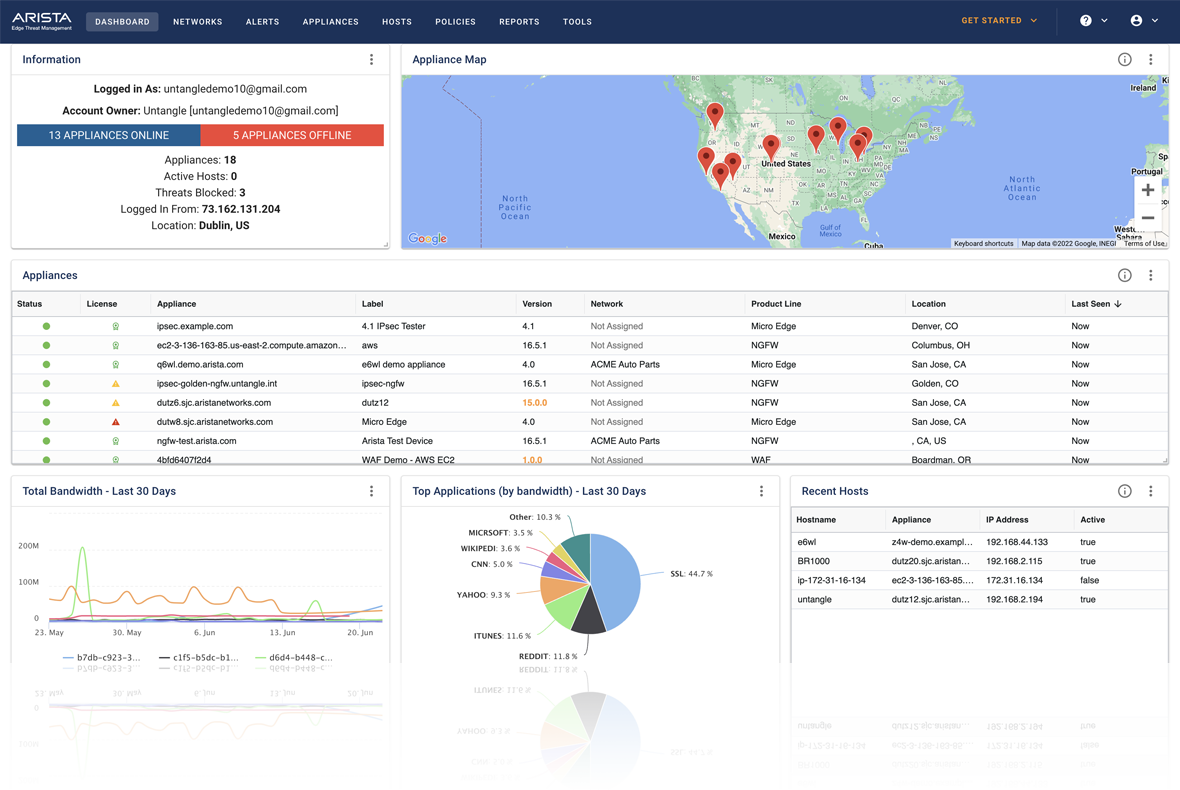
ETM Dashboard
Cloud-based Centralized
Management Platform
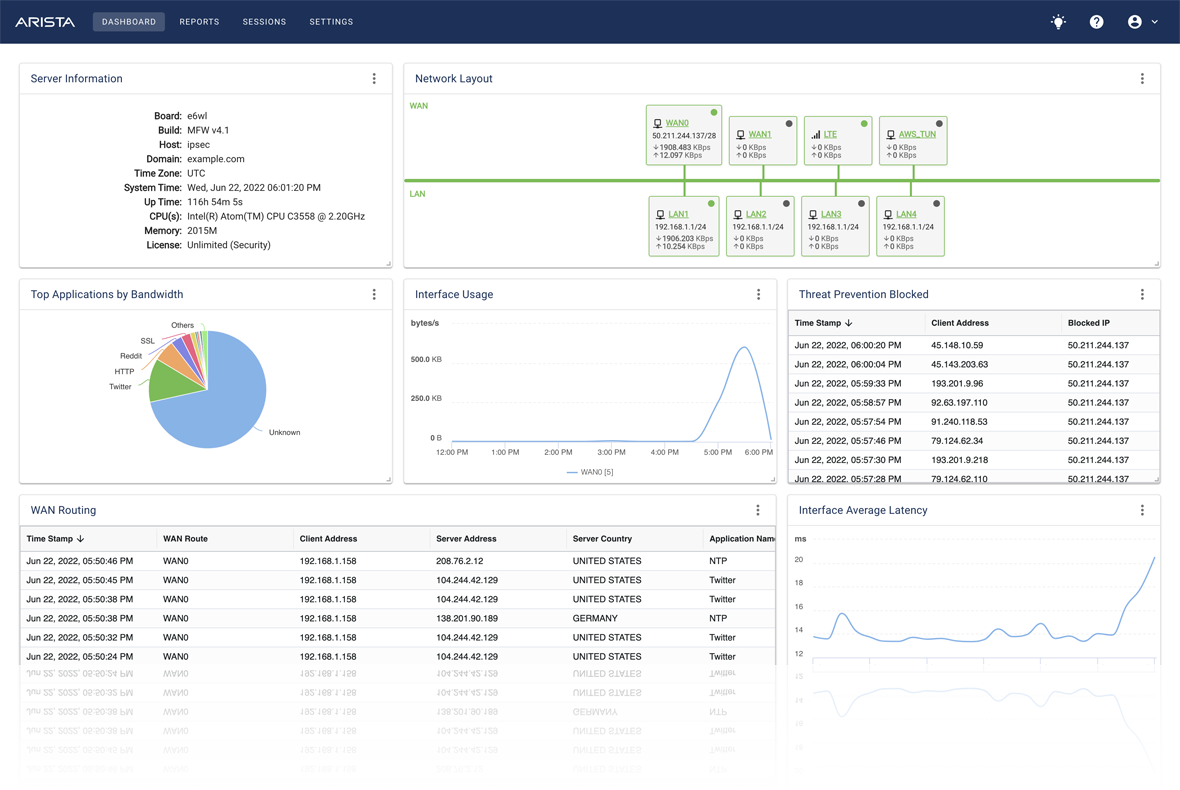
MICRO EDGE
Lightweight Network-edge Device
for Branch Office Connectivity
Your Industry. Your Network.
NG Firewall is the
#1 Choice of IT Pros
We understand that you have a choice between many competing network security solutions. We’re confident, however, that you won’t find another corporate partner more committed to your success than us.


You Could Qualify
for Special Pricing
Special pricing is available to qualifying public schools, libraries, state and local government institutions, NGOs, private schools, religious organizations and other not-for-profit institutions.
The Cognitive
Unified Edge
Edge Threat Management is a key component of The Cognitive Unified Edge (CUE) from Arista Networks. CUE enables commercial customers to accelerate new services and technology innovations by consolidating multiple security and networking functions into an “edge as a service” cloud-managed solution. CUE provides plug and play simplicity and workflows for small enterprise LAN, Wi-Fi, security, and micro WAN connectivity services.

Appliances Designed for you

Hardware
Appliances
Dedicated hardware appliances provide extensive control of the network, visibility into traffic and events, flexible connectivity options, and multiple layers of advanced protection. Appliances are shipped with NG Firewall or Micro Edge pre-installed, ready for zero touch provisioning and are available in a variety of sizes to fit networks from small to large.
Recognized Leader in Cybersecurity
Stay Up to Date
Sign up to receive updates on news, products and more.
© 2024 Arista Networks, Inc. All rights reserved.