Tunnel VPN is the easiest way to create a persistent, secure connection between NG Firewall and a remote network. You can easily set up and manage a variety of network scenarios for a range of issues, such as:
- SD-WAN applications where you wish to create a virtual network overlay across multiple locations that make up your corporate network.
- Managing many small locations by redirecting all traffic through a central location
- Privacy or circumventing geographical limitations
Tunnel VPN is powered by a fully featured ruleset, enabling WAN optimizations around which traffic is sent through the tunnel and directed at any given interface, host, subnet, port or other criteria. Like other NG Firewall apps, Tunnel VPN uses a tagging feature to enable advanced, dynamic routing scenarios based on specified criteria.
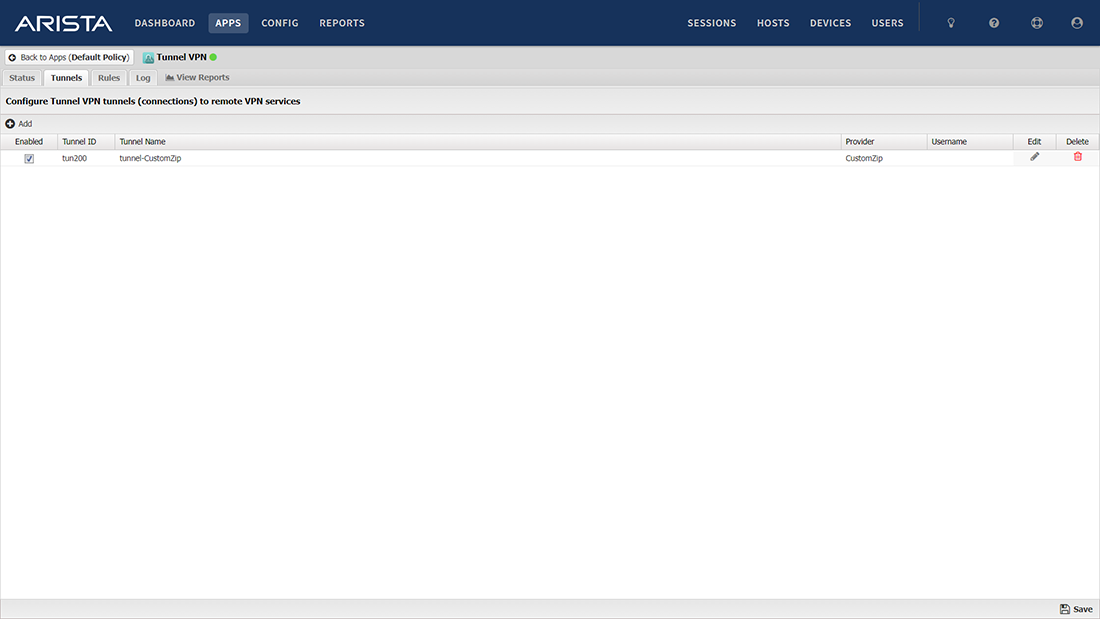
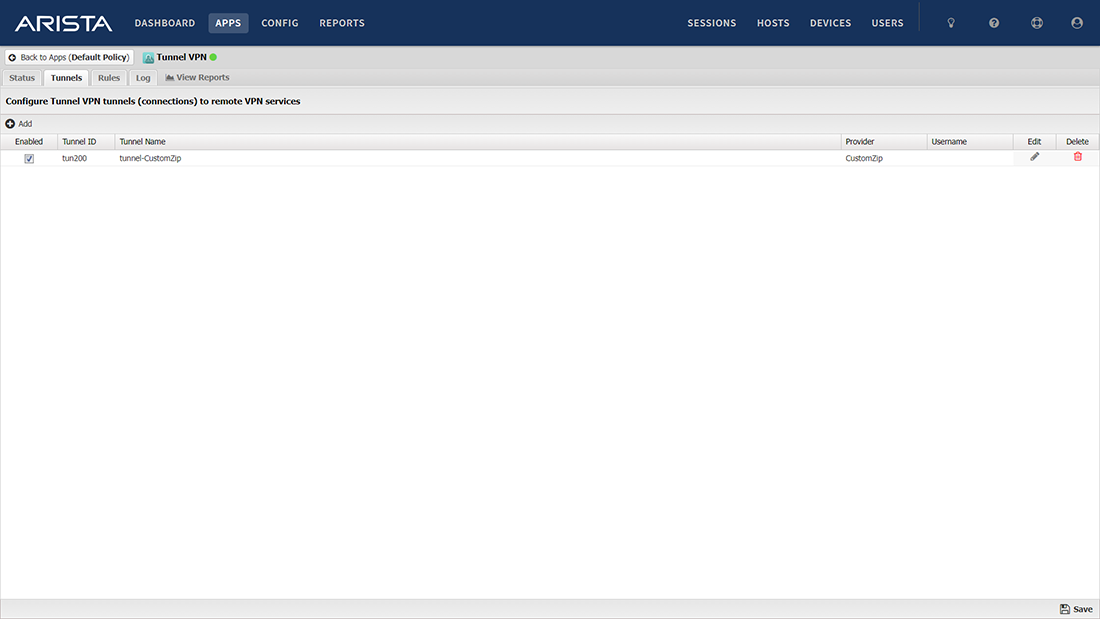
Tunnel VPN features a configuration wizard to enable connections to many privacy VPN providers like another ExpressVPN, NordVPN or even another NG Firewall. There are also generic options which support most commonly available OpenVPN-based providers.
Features
Configure all or selective traffic to be sent to cloud-based security services or Cloud Access Security Brokers (CASB)
Maintain multiple tunnel connections to several cloud exit points and prioritize tunnels to ensure a stable connection
Connect to popular privacy VPN services (NordVPN, Express) to create a private connection
Creates a safe encrypted passage to support a freer internet and net neutrality
Configure rules statically to force traffic through a tunnel (hosts or ports)
Configure rules dynamically to determine which traffic uses the tunnel via tags
Set up alerts for event statuses
Bind to specific WANs, allowing configuration of multiple tunnels for multi-WAN sites and ensuring each tunnel is using the desired physical WAN connection
Direct traffic to the most desirable WAN connection based on criteria like ports and protocols
Set up without NAT so that the cloud firewall has full visibility into the network
Get Tunnel VPN
Provide connectivity through encrypted tunnels to remote VPN servers and services.
Provide connectivity through encrypted tunnels to remote VPN servers and services.
NG Firewall makes life simple. It is easy to use and can be managed remotely, which is very important when there are eighteen locations to look after. Bruce Garner, Five Star Food Service
The Reports app is easy to use, and I can simply pull the required reports to show we are complying with CIPA. Jeff Olson, Vision Charter School
The new user interface is a nice improvement. The Dashboard provides me with a quick view of my network. David Phelps, Brown County Schools


